WHAT IS MFA?
Multi-factor Authentication has become an essential and preventative security measure for organizations and businesses as cyber crime is on the rise more than ever. Multi-factor authentication adds a critical layer of security that helps you protect data and resources, making it more difficult for hackers to breach the company network. Here’s everything you need to know about Multi-factor Authentication!
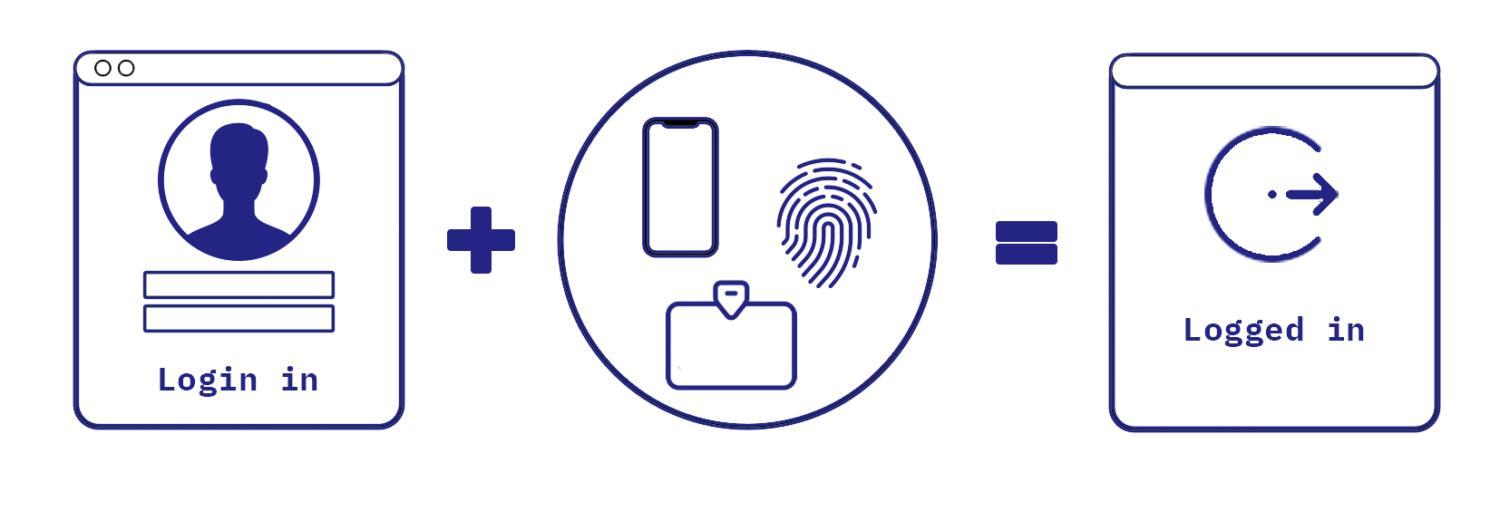
Multi-factor authentication (MFA) typically uses two or more independent access methods like passwords, security tokens or biometric verification. This creates a defense of multiple layers, which makes it much more difficult for an unauthorized person to access a protected system or application. This can be a computing device, a physical location a network, a website or a database.
STRENGTHEN YOUR SECURITY
Access methods like a password or a security questions can be hacked (or guessed) by brute-force or social engineering attacks. Over the last years and even more so recently, vast amounts of leaked, stolen credential sets (usernames, email addresses and passwords) have found their way onto the public internet. Even more credential sets are being sold on the dark web. By adding an additional access method (like an authenticator or fingerprint) it will be significant more difficult for the hacker to gain access to the desired asset.
“THE 3 TYPES OF ACCESS METHODES: KNOWLEDGE FACTORS, POSSESSION FACTORS AND BIOMETRIC FACTORS”
TYPES OF ACCESS METHODS
Within Multi-Factor Authentication there are 3 main types of authentication. By combining these different types a multi factor authentication is crafted. The 3 types are: Knowledge factors, Possession factors and Biometric factors.
KNOWLEDGE FACTORS
These are access methods which use something you know. These knowledge factors are the most commonly used type. The user has to prove he has the knowledge of some secret information. Methods like passwords, PINs and security questions fall into this category.
POSSESSION FACTORS
These are access methods which use something you have. Access methods where physical devices are needed make up this category. Examples are tokens, card readers, wireless tags, and certificates.
BIOMETRIC FACTORS
These are access methods which use something you are. This includes access methods that use any form of static biometrics like fingerprint readers, palm scanners, retina/iris scanners or facial patterns and dynamic biometrics like voice patterns, gait patterns or keyboard cadence. These factors are almost 100% unique to the authorised user and thus, biometric factors, can be seen as the most secure of the 3 types.
WHY SHOULD YOUR COMPANY USE MFA?
According to recent research, since the beginning of the year 2020, over 445 million cyber-attacks have been detected, which cost billions of dollars.
A common cyber-attack organizations have to deal with is when a websites login is attacked actively. If the hacker(s) are able to crack your password they will not be able to access your account because a 2nd access method is needed, which they will not be able to figure out. And that’s where MFA came into play, provided an added a layer of security and access management to the application.
It not only provides security but also helps with compliance, flexibility, and productivity. It gives the business owners an effective way to protect the infrastructure of their organization and adds multiple additional cybersecurity layers. Moreover, it is an effective cybersecurity approach that businesses of all sizes should use to boost their cloud security strategies. Above all, it is a low cost verified security solution that businesses can use to avoid data breach and significantly lowers the risk of account compromise attacks.
WHAT ARE THE ADVANTAGES OF MULTI-FACTOR AUTHENTICATION
IMPROVE SECURITY
The main advantage of MFA is identity assurance. The common identity theft threat scenarios by simple password theft are eliminated. Even if an attacker has the password, he still has no access to the system.
ACHIEVE COMPLIANCE
The other advantage of MFA is being able to achieve compliance requirements to the organization, which results in fewer audit findings and potential fines.
INCREASE FLEXIBILITY AND PRODUCTIVITY
As MFA complies with Single Sign-on (SSO) solutions it will increase flexibility and productivity, as a user no longer has to create multiple complex passwords on multiple websites and applications.
IN NEED OF A MULTI LAYER SECURITY?